Making Web Browsing Safer
Although the efforts of common web browsers are admirable in making the web a more secure, private place, they're not perfect. Today I'm going to be sharing a couple of browser plugins that you can install to level up your privacy.

Although the efforts of common web browsers are admirable in making the web a more secure, private place, they're not perfect. Luckily, what they lack in privacy first features is easily fixed using a variety of plugins. Today I'm going to be sharing a couple that you can install to level up your privacy.
Before we begin, please be aware that the plugins below are only available to Google Chrome, Mozilla Firefox, Opera, and derivative browsers. Although Apple's Safari supports extensions, the extensions I am sharing today are not available in Safari; that said alternatives and unofficial versions may exist.
What are Plugins?
Web browsers are very large complex pieces of software used by pretty much anyone with an internet connection. With the billions of people using them comes a huge range of expectations, needs, and wants of functionality. Attempting to support all these functionalities would require huge amounts of effort for little gain.
Instead of building everything themselves, web browsers provide a series of interfaces that other developers can build upon. The resulting pieces of software are referred to as plugins - because they plug into the base browser, or extensions - as they extend the functionality of the browser.
The end result is a vast array of plugin ranging from integrating with useful services, adding ridiculous cosmetic changes, or changing core functionality.
A Word of Warning
Plugins are incredibly powerful and can make your web life significantly easier, however they can also pose a significant security threat.
When you install a plugin, you are granting a piece of software access to your browser, which may include full access to every web page you browse. Malicious and fake plugins do exist, so it is always worth doing due diligence to ensure that the plugin is produced by someone reputable and that you are getting the plugin you think you are.
If in doubt, don't install it!
Plugin #1: HTTPS Everywhere
When your web browser uses HTTPS, it establishes an encrypted connection between itself and the website you are browsing before transferring any content. This prevents any other actor from seeing or altering the data being transferred.
If someone can see the content, it is possible for them to steal confidential information such as passwords, credit cards, or personal information. This would include any Internet Service Provider (ISP) between you and the website you are connected to. It also includes anyone on your network which may be housemates, work colleagues, or in the case of public WiFi: strangers which may include malicious actors. In the case of ISPs, your traffic may also be mirrored to government agencies.
By using HTTP (which is unencrypted) you will also let anyone who carries your traffic to modify it as they see fit. Whilst ISPs have done this in the past, it usually isn't malicious because of the legal ramifications. However there are many people who setup "fake" public WiFi networks in order to intercept your traffic and/or deliver malware. Finally, there is the possibility that your home router has been infected with malware that could then snoop or modify your traffic.
Whilst most websites can be loaded over HTTPS, only 61% of the top 1 million websites default to HTTPS. This means that you may be left vulnerable to avoidable attacks. Web browsers do attempt to default to HTTPS but they're not perfect especially when dealing with copied links or links that specify HTTP. This can also include resources loaded in the background that may be on different domains to the page you just loaded (e.g. images, videos, ads).
This is where HTTPS Everywhere comes in. The plugin intercepts all web HTTP requests and attempts to upgrade them to HTTPS. In the event that the website does not support HTTPS at all, it will block the request.
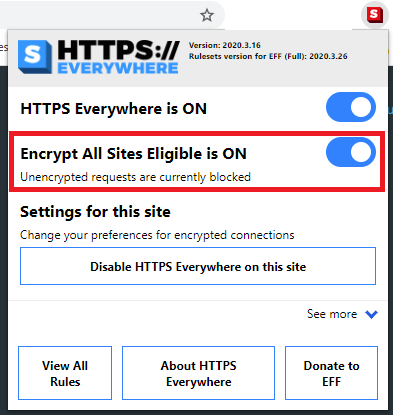
The plugin is very much set and forget unless a) you attempt to visit a HTTP only website, in which case you can make the decision to temporarily allow access. Or b) you encounter a HTTPS website that relies heavily on HTTP only resources which may appear broken.
HTTPS Everywhere is available for Chrome, Firefox, and Opera.
A special note on HTTPS
HTTPS ensures that the connection between your browser and the web server is encrypted and that the server is the domain that it says it is.
It does not protect against phishing attacks where a malicious actor will use a website that looks similar to the legitimate domain. Malicious actors can and do use HTTPS on their phishing sites.
Plugin #2: uBlock Origin
Most ad delivery and tracking occurs behind the scenes when you are browsing the web. This makes is difficult to prevent as you are never given the opportunity to stop these unwanted requests.
For the privacy conscious this is what allows advertisers like Google and Facebook to track you across the internet. It also will reveal large amounts of information about you from based on what sites you visit.
On the security side of things most of these requests will be pretty benign. However, ad platforms are often targeted by malicious actors which when successful leads to malvertising attacks where what was a safe website is now holding malware or even taking control of your browser.
uBlock Origin is a plugin that solves this issue by providing a way to block web requests based on rules. Fortunately there is no need to configure these rules yourself as it comes preloaded with a number of rules aimed at blocking ads and trackers - making it well known as an ad-blocker even though it can achieve more. Like HTTPS Everywhere it is also very much a set and forget plugin.
Blocking many of these extra web requests also has the added bonus of making your web browsing smoother by saving your bandwidth for the content you actually want and stopping the webpage from waiting for the ads to load. I'll note that it doesn't block all ads especially for smaller/ spammier websites that embed their own ads.
uBlock Origin is available for Chrome, Firefox, and Opera. There are also a number of unofficial versions including for Edge and Safari.
Mobile Browsers
Unfortunately not all mobile browsers support plugins, and those that do may not work with all plugins (it's not something I've tested). Chrome on mobile does not support any plugins so you would need to use an alternate browser such as Firefox or Brave (again I've not used these).